Protecting Your Data in the Cloud: Don't Use TrueCrypt
/Despite the recent discontinuation of TrueCrypt development under suspicious circumstances, TrueCrypt remains the preferred method of many people for creating encrypted storage containers. However, some of the characteristics of TrueCrypt containers that make them great for protecting your data also make them difficult to use with cloud storage services.
One of these characteristics is that TrueCrypt does not modify the timestamps of a container whenever its contents are changed. This is great for concealing actions taken surrounding your data, but it does not allow cloud storage sync clients that rely on the "Modified" timestamp to determine whether or not a file needs to be resynced to the cloud. OneDrive, my preferred cloud storage provider, is one of these services.
Here is how I tested this:
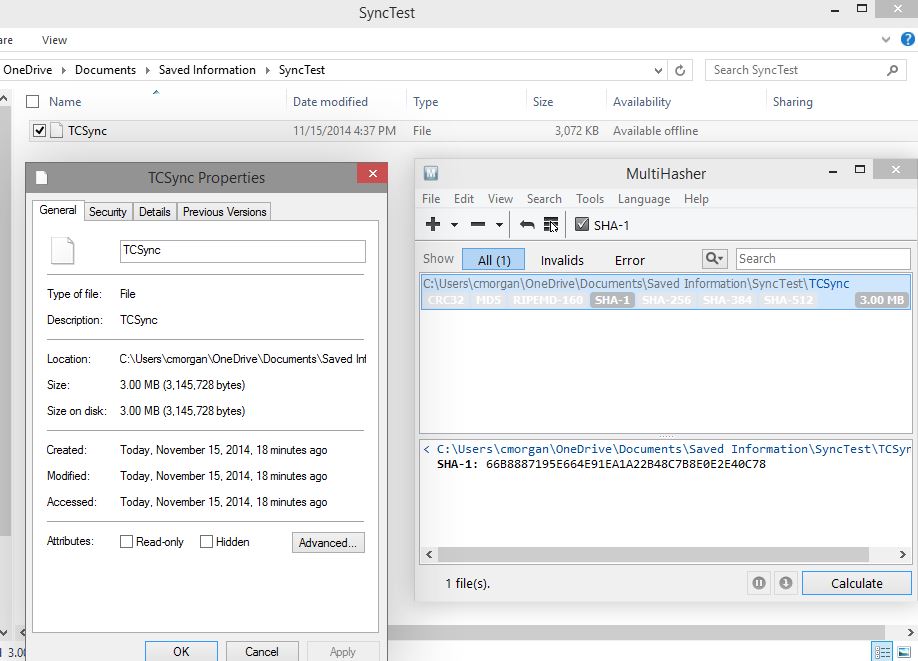
- I created a new, empty TrueCrypt container and placed it in my local OneDrive folder to be synced to the OneDrive service. Below, you will see the file with its accompanying timestamps and SHA-1 hash.
- I opened the OneDrive sync client and forced a sync to make sure it had checked for any changes and synced changed files.
- I mounted the container, created a test text file in the container, then unmounted the container. Below, you will see the container file with its updated SHA-1 hash, proving it has changed. However, the timestamps are clearly the same as when the file was created.
- After forcing a sync again through the OneDrive client, I went to the OneDrive website and downloaded the container file that was stored there.
- Mounting the downloaded container file showed that the container was still empty, as it was when the original file was synced to the OneDrive service.
This clearly shows that the OneDrive sync client relies on the "Modified" timestamp rather than file hashes to determine which files have changed and need to be synced back to the cloud service. Of course the workaround here is to use the OneDrive website to manually upload any TrueCrypt containers that have been changed, but that is clearly an inconvenience.
In future posts, I will be exploring other methods of protecting your data in the cloud.